“Nothing better than a big cup of tea in the morning.”
bird on the cup
becausebirds: feiens-snowden: “Nothing better than a big cup of tea in the morning.” bird on the cup
fauxboy: xekstrin: THE LITERAL BEST COMIC IVE EVER READ IN MY ENTIRE LIFE I laughed out loud
brocursion: *PLACEBO VOICE* THERE IS THUNDER IN OUR HEARTS BABY
Given that Chi-ji’s humanoid form is a blood elf (totally not spoilers because you learn this in chapter 2) how would Feiyn go about trying to touch his ears?
ever-brooding-prince-deactivate:
Tev: “Feiyn, that is not just a bird, that is Chi-Ji, the Red Crane of Hope.”
Feiyn, what?

Dk questions
So I figure I should get off my ass and start writing for my dk, but im a bit stuck on her story.
tl;dr would it be possible for her to die in northrend during WotLK and be raised as a DK- but still become a knight of the ebon blade?
Yes, Arthas was still raising and training new death knights as we laid seige to Icecrown. You can tell because there’s a group of Death Knight adepts and Initiates just a bit northeast of the entrance of Icecrown citadel where you’re sent on a quest to kill an NPC. (The Black Knight was also raised as a death knight.)
The Ebon Blade is still accepting undead freed from the Lich King, as well; as evidenced by the fact that the three NPCs that you end up freeing from Arthas’ control (Vile, Lady Nightswood, and The Leaper) as you take the Shadow Vault end up joining the Ebon Blade.
varae-ver-you-are: agent-hils-coulson: fishcustardandthecumberbeast: warrenworthingtonlll: youraveragebadass: cosmic-giganticat: youraveragebadass: Winter Soldier Easter egg in the first Captain America! nah man i looked through the movie to see and it isn’t Bucky its
Winter Soldier Easter egg in the first Captain America!
nah man i looked through the movie to see and it isn’t Bucky its just Peggy watching him go. she had the same hair and the Thompson and everything
I’m pretty sure it’s Bucky though. In an interview Sebastian Stan confirmed that the producers hid a very well hidden easter egg in a few frames in the film. Also the music tenses up during this scene which is gonna be weird considering Peggy was Steve’s bad ass love interest. So why would they play a dark tone when she would just come behind him? Also if you zoom in He’s wearing a mask??? I dunno I would put money on Bucky but your theory is as good as mine.
guys i just downloaded the movie and skipped to this part.
it is real.I have watched it and rewatched it and it looks like it’s real. At first I thought it was Peggy but you really can see the mask.
I don’t see how it’s not him.
MY MIND HAS JUST BLOWN OUT OF MY EARS PLEASE HELP
Because if you watch the actual scene, it is Peggy.
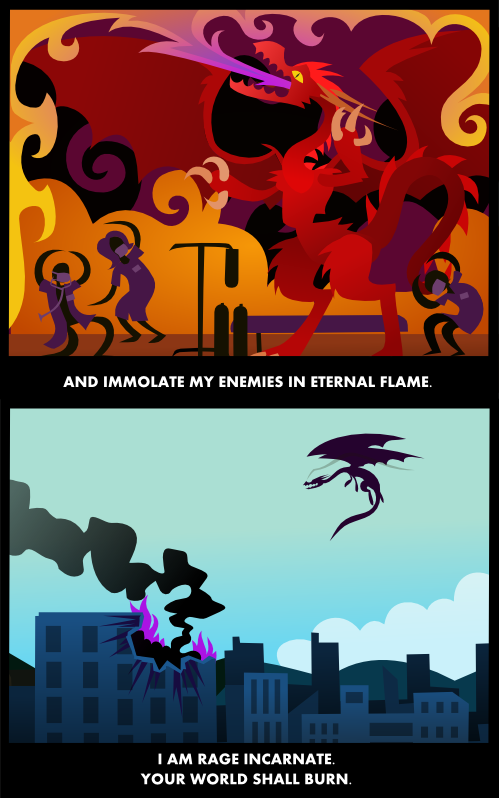
Given that Chi-ji’s humanoid form is a blood elf (totally not spoilers because you learn this in chapter 2) how would Feiyn go about trying to touch his ears?
ever-brooding-prince-deactivate:
Tev: “Feiyn, that is not just a bird, that is Chi-Ji, the Red Crane of Hope.”
Show of hands: who rps in game currency as being worth more than it actually is? like a couple silver could feed a family of four for a week. My warlock is absolutely LOADED but rarely carries more than thirty silver on her at a time.
The inflation is kinda cray in game mechanics, so yeh.
I do this as well. I think the only time I don’t exactly is if someone is RPing a lowbie character as a beggar (which, honestly— if you’re going to beg for gold, is the way to go; I like seeing some written effort), in which case I’ll emote my character pulling out a few silver pieces for them but actually trade them over 20g or so.
Because Oliver always gives to beggars. And muggers. Really, what’s a dead guy gonna do with money, buy food with it?
Same. And IC Tev’s loaded because people keep giving him money to kill stuff and he doesn’t know what to do with it. This is what happens when you’re dead and don’t have any fixed costs.
When a bad day gets worse—getting hacked twice in one day
moot:
Waking up to a string of missed calls is rarely a harbinger of good, and this time would prove no different. Upon returning the calls I was greeted with a simple “You’ve been hacked.” Great.
It turned out someone with my username had spent the morning causing a ruckus on 4chan. At first other users and moderators assumed I’d been drinking—at 7:00AM no less—but quickly concluded it was the work an intruder.
I immediately hopped out of bed and onto a call with our developer and a moderator to establish a timeline of events, and set about digging through error logs. It didn’t take long to piece together what had happened.
First, the intruder was able to enumerate files on a domain hosting moderator tools. He used an off-the-shelf script, and had the benefit of having leaked source code in his possession to build a site-specific wordlist.
Mistake #1: No rate limiting or HTTP auth dialog was present on the domain.
Most of the enumerated files did him no good since they made use of a PHP auth check, but one file was different: instead of displaying an error message, it simply bounced him to our front page. He manually set a 4chan admin username cookie (the cookie name gleaned from the source code), and voila, he was no longer redirected.
Mistake #2: The PHP auth check for this particular file was broken.
The page in question was a once-off used to generate statistics about reported posts. “0 days” was displayed on the page, and he guessed it might be a query parameter. He was correct, and as it turned out this one parameter was vulnerable to SQL injection. After some more testing, he realized he was able to return information from our database using the error messages displayed.
Mistake #3: Unescaped SQL query, and not disabling MySQL errors in production.
Using the injection vulnerability, he was able to exfiltrate information from our backend database. Thankfully we have a record of all information accessed (thanks to those handy error messages being logged), and it appears he mostly poked around before settling on accessing moderator credentials. He took my username and password, set them in his cookies, confirmed they worked by visiting an admin panel on the main site, and began lurking.
Mistake #4: Boneheaded cookie auth—we simply stored the bcrypted password from the database in a cookie, which was all that was required to pass PHP auth.
After lurking for a few days, the intruder decided to make himself known by publicly shaming a user under my username. He later stated this was his motivation for gaining entry all along—to out a user he disliked. Using admin panels, he was able to obtain and leak information about other users, as well as moderator names and IP addresses.
We quickly patched the vulnerability, forced a password reset for all moderator accounts, and have spent the past two weeks reviewing our code and servers to apply fixes and make improvements where possible.
The day didn’t end there though. This next bit concerns DrawQuest.
I loaded my e-mail for the first time that morning, and at the top of the list was a message from Amazon: “Unauthorized activity in your AWS account”
To make an already long story short, when leaving the company a few months ago, one of our developers asked to open source a project he had worked on. You can probably already guess where this is going, but suffice it to say he did so by flipping the existing repository to public.
Despite having overwritten our AWS keys, they were still available in the commit history and likely recovered by a bot. An intruder was able to use them to create an administrator account, giving them access to our AWS dashboard, and used it to spin up a hundred extra-large instances—probably for Bitcoin mining. They also would have had access to all of our S3 buckets, EC2 and RDS instances, DNS, etc.
Mistake #5: Not creating a fresh repo for a newly open sourced project, or at least scrubbing commit history.
Mistake #6: Using a highly-privileged key where a lesser-privileged one would have sufficed.
For DrawQuest, this was catastrophic. Despite our team going their separate ways a few months ago, we’d hoped to continue operating the app using the company’s remaining capital. However without any full-time employees left on staff, after the breach we felt the only responsible path forward was to shutter the service completely since we lack the time and resources to do a complete audit in order to ensure the integrity of our servers and Amazon account.
And so last night, with a lump in my throat, I announced that we’d be shutting down DrawQuest—a beloved drawing community that still boasted 100,000 monthly active users.
It was a long day to say the least.
On one hand I’m frustrated we made such simple mistakes that resulted in very real consequences, but also grateful that it provided us an opportunity to learn from those mistakes, and share them with the world.
There’s no silver bullet when it comes to security, and the only way to stay ahead of it is constant vigilance. Don’t rely on any one method to protect your service, assume the methods you already have in place don’t work, adhere to best practices, and make it a point to revisit security on a regular basis—not just when something goes terribly wrong.
To that end and in keeping with our ongoing commitment to security, I’m pleased to announce the launch of 4chan’s Vulnerability Disclosure Program. It’s my hope that by embracing responsible disclosure and providing an officially sanctioned way for security researchers to submit such reports, we’ll be in a better position to avoid or at least mitigate future incidents.
In the end, I accept full responsibility for both breaches. I wasn’t ever involved on the technical side for DrawQuest and don’t actively write code for 4chan any longer, but know it was ultimately my responsibility as founder and CEO to ensure the security of both. I’m very sorry to both communities that I failed in that capacity.
If I’ve learned anything from this experience, it’s that if you don’t treat security as a top priority, it will bite you. It’s not a matter of if—only when.